Lab 4.1.2 Characterizing Network Applications
Step 1: Cable and configure the current network
a. Connect and configure the devices in accordance with the topology and configuration given.
For this lab, a PC workstation can substitute for a Discovery Server.
b. Ping between Host 1 and Discovery Server to confirm network connectivity.
Troubleshoot and establish connectivity if the pings fail.
Step 2: Configure NetFlow on the interfaces
NetFlow is configured to monitor data flows in or out of specific router interfaces. Ingress captures traffic that
is being received by the interface. Egress captures traffic that is being transmitted by the interface. In this lab,
the traffic will be monitored on both router interfaces and in both directions from within the console session.
a. From the global configuration mode, issue the following commands:
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow ?
Note the two options available:
egress Enable outbound NetFlow
ingress Enable inbound NetFlow
Which option captures traffic that is being received by the interface? ingress
Which option captures traffic that is being transmitted by the interface? egress
b. Complete the NetFlow configuration.
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#exit
FC-CPE-1(config)#end
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode, issue the show running-configuration command.
For each FastEthernet interface, what statement from the running-configuration denotes that NetFlow
is configured?
interface FastEthernet0/0:
ip flow ingress
ip flow egress
interface FastEthernet0/1:
ip flow ingress
ip flow egress
b. From the privileged EXEC mode, issue the command:
FC-CPE-1#show ip flow ?
Note the three options available:
export Display export
Statistics
interface Display flow
configuration on Interfaces
top-talkers Display top talkers
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
Step 4: Create network data traffic
a. The captured data flow can be examined using the show ip cache flow command issued from
the privileged EXEC mode.
FC-CPE-1#show ip cache flow
Issuing this command before any data traffic has flowed should produce output similar to the example
shown here.
IP packet size distribution (0 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 0 bytes
0 active, 0 inactive, 0 added
0 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
last clearing of statistics never
Protocol Total Flows Packets Bytes Packets Active(Sec)
Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
SrcIf SrcIPaddress DstIf DstIPaddress Pr SrcP DstP
Pkts
b. List the seven highlighted column headings and consider what use this information may be in
characterizing the network.
Protocol
Total Flows
Flows per Second
Packets per Flow
Bytes per Packet
Packets per Second
Seconds of active flow
Seconds of no flow (idle)
c. To ensure that flow cache statistics are reset, from privileged EXEC mode issue the command:
FC-CPE-1# clear ip flow stats
d. Ping the Business Server from Host 1 to generate a data flow.
From the command line of Host 1, issue the command ping 172.17.1.1 -n 200
Step 5: View the data flows
a. At the conclusion of the data flow, the details of the flow can be viewed. From privileged EXEC mode,
issue the command:
FC-CPE-1#show ip cache flow
Output similar to that shown below will be displayed. Some values and details may be different in
your lab.
IP packet size distribution (464 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .900 .096 .000 .000 .000 .000 .002 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
5 active, 4091 inactive, 48 added
1168 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 17416 bytes
0 active, 1024 inactive, 0 added, 0 added to flow
0 alloc failures, 0 force free
1 chunk, 1 chunk added
last clearing of statistics never
Protocol Total Flows Packets Bytes Packets Active(Sec)
Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow
/Flow
UDP-DNS 31 0.0 1 72 0.0 0.0
15.5
UDP-other 10 0.0 2 76 0.0 4.1
15.2
ICMP 2 0.0 200 60 0.3 198.9
15.3
Total: 43 0.0 10 61 0.3 10.2
15.5
SrcIf SrcIPaddress DstIf DstIPaddress Pr SrcP DstP
Pkts
< output omitted >
b. Examine your output and list details that indicate data flow.
Protocol
Total Flows
Flows per Second
Packets per Flow
Bytes per Packet
Packets per Second
Seconds of active flow
Seconds of no flow (idle)
Step 6: Stop the NetFlow capture
a. To deactivate NetFlow capture, issue the no ip flow command at the interface configuration
prompt.
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#no ip flow ingress
FC-CPE-1(config-if)#no ip flow egress
FC-CPE-1(config)#interface fastethernet 0/1
FC-CPE-1(config-if)#no ip flow ingress
FC-CPE-1(config-if)#no ip flow egress
b. To verify that NetFlow is deactivated, issue the show ip flow interface command from the
privileged EXEC mode.
FC-CPE-1#show ip flow interface
FC-CPE-1#
No output is displayed if NetFlow is off.
Step 7: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts
that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the
appropriate cabling and restore the TCP/IP settings.
Step 8: Reflection
Consider the possible range of data flow types across a network and how a tool like NetFlow could be
implemented to assist in analyzing those flows.
List of data flow categories and types: Client to Client, Client to Server, Server to Client, and Server to Server
Email, intranet web, database flows, document file flows
Number of separate flows of each type, size (bytes) of each flow, time each flow is on the network
Daftar kategori dan jenis aliran data: Client untuk Klien, Klien ke Server, Server untuk Client, dan Server ke Server
Email, web intranet, aliran database, file dokumen arus
Jumlah arus yang terpisah masing-masing jenis, ukuran (bytes) dari setiap aliran, waktu setiap aliran pada jaringan
Email, web intranet, aliran database, file dokumen arus
Jumlah arus yang terpisah masing-masing jenis, ukuran (bytes) dari setiap aliran, waktu setiap aliran pada jaringan
Final Configurations
Router 1
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption!
hostname FC-CPE-1!
boot-start-marker
boot-end-marker!
enable password cisco!
no aaa new-model
ip cef!
interface FastEthernet0/0
ip address 10.0.0.1 255.255.255.0
ip flow ingress
ip flow egress
duplex auto
speed auto
interface FastEthernet0/1
ip address 172.17.0.1 255.255.0.0
ip flow ingress
ip flow egress
duplex auto
speed auto
interface Serial0/1/0
no ip address
shutdown
no fair-queue
clock rate 2000000
!
interface Serial0/1/1
no ip address
shutdown
clock rate 2000000
ip http server
no ip http secure-server
control-plane
line con 0
password cisco
login
line aux 0
line vty 0 4
password cisco
login
scheduler allocate 20000 1000
end
Lab 4.2.3 Analyzing Network Traffic
Task 1: Design Network Access to FTP and Email Services
Step 1: FTP network considerations
File transfer traffic can put high-volume traffic onto the network. This traffic can have a greater effect on
throughput than interactive end-to-end connections. Although file transfers are throughput-intensive, they
typically have low response-time requirements. As part of the initial characterization of the network, it is important to identify the level of FTP traffic that will be generated. From this information, the network designers can decide on throughput and redundancy requirements.
a. List possible file transfer applications that would generate traffic on the FilmCompany network.
Document sharing
Video production file transfer
b. List these applications by priority based on response time.
1. Video production file transfer
2. Document sharing
c. List these applications by priority based on bandwidth requirements.
1. Video production file transfer
2. Document sharing
Step 2: Email network considerations
Although customers expect immediate access to their emails, they usually do not expect emails to have
network priority over files that they are sharing or updating. Emails are expected to be delivered reliably and accurately. Generally, emails are not throughput-intensive, except when there are enterprise-wide mail-outs or there is a denial of service attack.
List some email policies that could control the volume of email data and the bandwidth used.
Membatasi ukuran lampiran email
Membatasi nomor penerima pesan email
Memastikan spam terfilter sebelum menjangkau LAN
Step 3: Configure and connect the host PCs
a. Set the IP addresses for PC1 and PC2 as shown in the configuration table.
b. Establish a terminal session to router R1 from one of the PCs, and configure the interfaces and
hostname as shown in the configuration table.
Task 2: Configure NBAR to Examine Network Traffic
Step 1: Enable NBAR Protocol Discovery
NBAR can determine which protocols and applications are currently running on a network. NBAR includes the
Protocol Discovery feature, which identifies the application protocols operating on an interface so that
appropriate QoS policies can be developed and applied. To enable Protocol Discovery to monitor selected
protocols on a router interface, issue the following commands from the global configuration mode:
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip nbar protocol-discovery
Step 2: Confirm that Protocol Discovery is configured
From the privileged EXEC mode, issue the show running-config command and confirm that the following
output appears under interface FastEthernet 0/0:
interface FastEthernet0/0
ip address 10.0.0.1 255.255.255.0
ip nbar protocol-discovery
If protocol-discovery is not confirmed, reissue the configuration commands for interface FastEthernet
0/0.
Task 3: Generate and Identify Network Traffic
Step 1: Generate FTP traffic
The Mozilla Thunderbird email client program will be downloaded from Discovery Server as an example of FTP.
a. On PC1, launch a web browser and enter the URL ftp://server.discovery.ccna,
Alternatively, from the command line, enter ftp server.discovery.ccna. If DNS is not
configured the IP address 172.17.1.1 must be used instead of the domain name.
b. Locate the file thunderbird_setup.exe in the pub directory, download the file, and save it on PC1.
Repeat this step for PC2.
Step 2: Generate Email traffic
If the Thunderbird email client has been installed and email accounts set up on both PC1 and PC2, proceed
to Step 2d. Otherwise, install and set up the email client on PC1 and PC2 as described in Steps 2a through 2c.
a. Install the Thunderbird email client on PC1 and PC2 by double-clicking the downloaded
thunderbird_setup.exe file and accepting the default settings.
b. When the installation has completed, launch the program.
c. Configure email account settings as shown in this table.
1) On the Tools menu, click Account Settings
Complete the required Thunderbird Account Settings.
In the left pane of the Account Settings screen, click Server Settings and complete the
necessary details.
4) In the left pane, click Outgoing Server (SMTP) and complete the proper configuration for the
Outgoing Server (SMTP).
d. Send and receive two emails between accounts on each PC.
Step 3: Display the NBAR results
With Protocol Discovery enabled, any protocol traffic supported by NBAR, as well as the statistics associated
with that protocol, can be discovered.
a. To display the traffic identified by NBAR, issue the show ip nbar protocol-discovery
command from the privileged EXEC mode.
FC-CPE-1#show ip nbar protocol-discovery
b. List each protocol identified and the Input and Output information.
Output:
ftp 18 16
1295 1288
0 0
0 0
c. Although the data traffic in this lab may not be sufficient to generate values for the 5min Bit rate
(bps) and 5min Max Bit Rate (bps) fields, consider and discuss how these values would be applied
to designing an FTP and email network.
Dapat membantu menentukan rata-rata dan puncak kebutuhan bandwidth jaringan.
Step 4: Use NBAR to monitor other data traffic
NBAR can identify and monitor a range of network application traffic protocols.
From the privileged EXEC mode of the router, issue the command show ip nbar port-map and note the output displayed.
FC-CPE-1#show ip nbar port-map
List some protocols that you consider should be monitored and policies applied to.
Output
port-map bgp udp 179
port-map bgp tcp 179
port-map bittorrent tcp 6881 6882 6883 6884 6885 6886
6887 6888 6889
port-map citrix udp 1604
port-map citrix tcp 1494
port-map cuseeme udp 7648 7649 24032
port-map cuseeme tcp 7648 7649
port-map dhcp udp 67 68
port-map directconnect tcp 411 412 413
port-map dns udp 53
port-map dns tcp 53
port-map edonkey tcp 4662
port-map exchange tcp 135
port-map fasttrack tcp 1214
port-map finger tcp 79
port-map ftp tcp 21
port-map gnutella udp 6346 6347 6348
port-map gnutella tcp 6346 6347 6348 6349 6355 5634
port-map gopher udp 70
port-map gopher tcp 70
port-map h323 udp 1300 1718 1719 1720 11720
port-map h323 tcp 1300 1718 1719 1720 11000 – 11999
port-map http tcp 80
port-map imap udp 143 220
port-map imap tcp 143 220
port-map irc udp 194
port-map irc tcp 194
port-map kerberos udp 88 749
port-map kerberos tcp 88 749
port-map l2tp udp 1701
port-map ldap udp 389
port-map ldap tcp 389
port-map mgcp udp 2427 2727
port-map mgcp tcp 2427 2428 2727
port-map netbios udp 137 138
port-map netbios tcp 137 139
port-map netshow tcp 1755
port-map nfs udp 2049
port-map nfs tcp 2049
port-map nntp udp 119
port-map nntp tcp 119
port-map notes udp 1352
port-map notes tcp 1352
port-map novadigm udp 3460 3461 3462 3463 3464 3465
port-map novadigm tcp 3460 3461 3462 3463 3464 3465
port-map ntp udp 123
port-map ntp tcp 123
port-map pcanywhere udp 22 5632
port-map pcanywhere tcp 65301 5631
port-map pop3 udp 110
port-map pop3 tcp 110
port-map pptp tcp 1723
port-map printer udp 515
port-map printer tcp 515
port-map rcmd tcp 512 513 514
port-map rip udp 520
port-map rsvp udp 1698 1699
port-map rtsp tcp 554
port-map secure-ftp tcp 990
port-map secure-http tcp 443
port-map secure-imap udp 585 993
port-map secure-imap tcp 585 993
port-map secure-irc udp 994
port-map secure-irc tcp 994
port-map secure-ldap udp 636
port-map secure-ldap tcp 636
port-map secure-nntp udp 563
port-map secure-nntp tcp 563
port-map secure-pop3 udp 995
port-map secure-pop3 tcp 995
port-map secure-telnet tcp 992
port-map sip udp 5060
port-map sip tcp 5060
port-map skinny tcp 2000 2001 2002
port-map smtp tcp 25
port-map snmp udp 161 162
port-map snmp tcp 161 162
port-map socks tcp 1080
port-map sqlnet tcp 1521
port-map sqlserver tcp 1433
port-map ssh tcp 22
port-map streamwork udp 1558
port-map sunrpc udp 111
port-map sunrpc tcp 111
port-map syslog udp 514
port-map telnet tcp 23
port-map tftp udp 69
port-map vdolive tcp 7000
port-map winmx tcp 6699
port-map xwindows tcp 6000 6001 6002 6003
Step 5: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings
Challenge
This lab considered only the volume of FTP and email data traffic and its impact on network design. Reliable
access to servers is also important. In the space below, sketch a revised topology for this lab that would
provide redundancy for these services.
Lab 4.3.3 Prioritizing Traffic
Step 1: Gather the data traffic information
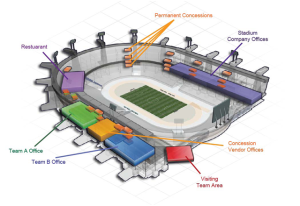
a. Read through the StadiumCompany case study curriculum.
List the current types of data traffic carried by the StadiumCompany network as well as the types
planned for the future.
List the possible data sources and destinations on the StadiumCompany network. For example, there
is likely to be data communications between the stadium management and the vendor management,
but not between Team A and Team B.
Step 2: Prioritize the data traffic
- List the source, destination, and traffic type that will be assigned the High priority queue.
- List the source, destination, and traffic type that will be assigned the Medium priority queue.
- List the source, destination, and traffic type that will be assigned the Normal priority queue
- List the source, destination, and traffic type that will be assigned the Low priority queue.
Step 3: Finalize the Data Priorities
a. Discuss and review your data priority assignments with another student to ensure that it addresses allnpossible data. Modify your priorities as necessary.
b. Highlight on the StadiumCompany topology diagram the device or devices where data traffic priority policies are likely to be configured.
Step 4: Reflection
Ideally, it may seem that all data traffic should be given a priority and queued accordingly. Consider and
discuss the potential for network performance to be negatively affected if this policy were implemented
everywhere on the network.
Delay data sensitif akan melihat prioritas yang sama sebagai non-delay data sensitif. Suara, video, diberi prioritas yang sama sebagai lalu lintas lainnya, dll
Lab 4.3.4 Exploring Network QoS
Step 1: Cable and configure the network
a. Connect and configure the devices in accordance with the given topology and configuration.
Routing will have to be configured across the serial WAN link to establish data communications.
Configure Telnet access on each router.
b. Ping between Host1 and Discovery Server to confirm network connectivity.
1) Confirm Application Layer connectivity by telnetting from R2 to R1.
2) Troubleshoot and establish connectivity if the pings or Telnet fail.
c. After confirming the initial configurations, maintain a console terminal session connection with R2.
Step 2: Examine priority queue commands
Configuring Priority Queueing
Configuring priority queueing (PQ) has two required steps and an optional third step:
1. Define the priority list (Required)
2. Assign the priority list to an Interface (Required)
3. Monitor priority queueing lists (Optional)
A priority list contains the definitions for a set of priority queues. The priority list specifies which queue a
packet will be placed in and, optionally, the maximum length of the different queues. To perform queueing
using a priority list, you must assign the list to an interface. The same priority list can be applied to multiple interfaces. Alternatively, you can create many different priority policies to apply to different interfaces.
Defining the Priority List
The priority list is defined by:
1. Assigning packets to priority queues
2. Specifying the maximum size of the priority queues (Optional)
Packets are assigned to priority queues based on the protocol type and the interface where the packets enter the router. The priority-list commands are read in order of appearance until a matching protocol or interface type is found. When a match is found, the packet is assigned to the appropriate queue and the search ends. Packets that do not match other assignment rules are assigned to the default queue. The following global configuration mode commands are used to specify in which queue a packet is placed. The command format is priority-list list-number Use a list-number of 1 and note the options available.
a. Enter the following command and note the options available.
FC-CPE-1(config)#priority-list 1 ?
default Set priority queue for
unspecified datagrams
interface Set priorities for packets
from a named interface
protocol priority queueing by protocol
queue-limit Set queue limits for
priority queues
b. Note some of the protocol options available.
FC-CPE-1(config)#priority-list 1 protocol ?
arp IP ARP
bridge Bridging
cdp Cisco Discovery Protocol
compressedtcp Compressed TCP (VJ)
http HTTP
ip IP
llc2 llc2
pad PAD links
pppoe PPP over Ethernet
snapshot Snapshot routing support
c. Note the IP protocol options available.
FC-CPE-1(config)#priority-list 1 protocol ip ?
high
medium
normal
low
d. Note the HTTP protocol options available.
FC-CPE-1(config)#priority-list 1 protocol http ?
high
medium
normal
low
e. Note the IP protocol high priority options available.
FC-CPE-1(config)#priority-list 1 protocol ip high ?
fragments Prioritize fragmented IP
packets
gt Prioritize packets greater
than a specified size
list To specify an access list
lt Prioritize packets less than a
specified size
tcp Prioritize TCP packets ‘to’ or
‘from’ the specified port
udp Prioritize UDP packets ‘to’ or
‘from’ the specified port<cr>
f. Note the IP protocol high priority TCP options available.
FC-CPE-1(config)#priority-list 1 protocol ip high tcp ?
<0-65535> Port number
domain Domain Name Service (53)
echo Echo (7)
ftp File Transfer Protocol (21)
ftp-data FTP data connections (20)
irc Internet Relay Chat (194)
nntp Network News Transport Protocol
(119)
pop3 Post Office Protocol v3 (110)
smtp Simple Mail Transport Protocol
(25)
telnet Telnet (23)
www World Wide Web (HTTP, 80)
Over 30 port/service options are available.
Step 3: Configure an example priority queue
From the global configuration mode, issue the following commands.
FC-CPE-1(config)#priority-list 1 protocol http high
FC-CPE-1(config)#priority-list 1 protocol ip normal tcp ftp
FC-CPE-1(config)#priority-list 1 protocol ip medium tcp telnet
What do these commands establish?
Sebuah daftar prioritas (nomor “1″) yang menetapkan paket HTTP yang akan ditandai sebagai prioritas tinggi, paket FTP rendah prioritas, dan Telnet paket sebagai prioritas menengah.
Step 4: Assign the priority list to an interface
a. From the global configuration mode, issue the following commands to assign the priority list to
interface serial 0/1/0.
FC-CPE-1(config)#int s0/1/0
FC-CPE-1(config-if)#priority-group 1
b. Confirm the priority list configuration. From the privileged EXEC mode, issue the show runningconfig
command.
Which statements in the configuration show that the priority list has been configured and applied
correctly?
interface Serial0/1/0
ip address 10.10.0.2 255.255.255.252
priority-group 1
priority-list 1 protocol http high
priority-list 1 protocol ip normal tcp ftp
priority-list 1 protocol ip medium tcp telnet
c. Confirm that issuing the show queueing priority command from the privileged EXEC mode
produces the following output:
FC-CPE-1#show queueing priority
Current DLCI priority queue configuration:
Current priority queue configuration:
List Queue Args
1 high protocol http
1 normal protocol ip tcp port ftp
1 medium protocol ip tcp port telnet
Step 5: Examine the priority queues operation
a. On Host1, launch a web browser and enter the URL http://172.17.1.1 to access the web
services configured on the server.
b. Use FTP to download a file. On Host1, launch a new web browser window and enter the URL
ftp://172.17.1.1, or from the command line issue ftp 172.17.1.1
c. Download a large file from the server; for example, the Thunderbird setup program file.
d. From the privileged EXEC mode, issue the following command:
FC-CPE-1#show queueing interface s0/1/0
Output similar to this should be displayed:
Interface Serial0/1/0 queueing strategy: priority
Output queue utilization (queue/count)
high/94 medium/0 normal/106759 low/0
Note the packet count for each queue:
High
Medium
Normal
Low
e. Initiate a Telnet session from R2 to R1 and issue some show commands on R1.
f. Close the Telnet session.
g. Issue the following command from the R2 privileged EXEC mode:
FC-CPE-1#show queueing interface s0/1/0
Note the packet count for each queue:
High
Medium
Normal
Low
What is the significant difference when compared to the previous output form this command in
Step 5d?
Antrian Menengah sekarang memiliki jumlah paket, ini adalah prioritas yang ditugaskan untuk paket Telnet.
Step 6: Determine the priority queue requirements for the case study
a. Using the FilmCompany case study, what would you expect the priority queue requirements to be?
b. Discuss and compare your priorities with other students.
c. Amend your priority list statements to include traffic associated with the proposed network upgrade.
Step 7: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts
that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the
appropriate cabling and restore the TCP/IP settings.
Challenge
The following privileged EXEC command displays the contents of packets inside a queue for a particular
interface:
show queue interface-type interface-number
However, in this lab, it is not likely that sufficient data traffic was generated at one time for the interface
queues to hold packets long enough to be inspected. Discuss how a network has to be load tested to ensure that all traffic priorities are met.
Lab 4.4.4 Investigating Video Traffic Impact on a Network
Step 1: Cable and configure the network
a. Connect and configure the devices in accordance with the given topology and configuration.
Set clock rate on the serial link to 56000.
Routing will have to be configured across the serial WAN link to establish data communications.
Step 2: Observe data traffic
In this step, you will generate concurrent data traffic and observe the time the flows take.
a. From Host1 command line, issue the command ping 172.17.1 1 –n 500 to generate a large
number of pings to Discovery Server.
b. While the pings are being generated on Host1, launch a web browser and enter the URL
http://server.discovery.ccna or http://172.17.1.1 to access the web services
configured on the server.
c. Use FTP to download a file. On Host1, launch a new web browser window and enter the URL
ftp://server.discovery.ccna, or issue ftp server.discovery.ccna from the command
line. If DNS is not configured, the IP address 172.17.1.1 must be used instead of the domain name.
d. Download a large file from the server; for example, the Thunderbird setup program file.
Note the total time taken to complete the pings, access the web page, and download the file.
Step 3: Stream the video file
Before beginning to stream the video ensure that QuickTime Player is installed on Host1, and that the video streaming service has been enabled on Discovery Server. See your instructor for advice if you are unsure. Launch QuickTime Player. Under File menu, go to Open URL
Enter URL rtsp://172.17.1.1/MWO.sdp, or a URL as provided by the instructor.
Note rate at which it plays back and the video and sound quality.
Video Quality
Sound Quality
Step 4: Observe both video and data traffic
a. From Host1 command line, issue the command ping 172.17.1 1 –n 500 to generate a large
number of pings to Discovery Server.
b. While the pings are being generated, use QuickTime Player to access the streaming video URL
again.
c. While the video is being played, launch a new web browser window on Host1 and enter the URL
http://server.discovery.ccna or http://172.17.1.1 to access the web services
configured on the server.
d. On Host1, launch another web browser window and enter the URL
ftp://server.discovery.ccna, or issue ftp server.discovery.ccna from the command
line. If DNS is not configured, the IP address 172.17.1.1 must be used instead of the domain name.
e. Download a large file from the server; for example, the Thunderbird setup program file.
Note the total time taken to complete the pings, access the web page, and download the file.
Note rate at which it plays back and the video and sound quality.
Video Quality
Sound Quality
Step 5: Observe the data flows with a different serial link clock rate
a. Change the serial link clock rate to 250000 on the router with the DCE interface.
b. Repeat Step 4 and record your observations.
Note the total time taken to complete the pings, access the web page, and download the file.
Note rate at which it plays back and the video and sound quality.
Video Quality
Sound Quality
c. Change the serial link clock rate to 2000000 on the router with the DCE interface.
d. Repeat Step 4 and record your observations.
Note the total time taken to complete the pings, access the web page, and download the file.
Note rate at which it plays back and the video and sound quality.
Video Quality
Sound Quality
Instructor Note: The Cisco 1841 router with WIC 2T Serial interfaces can support clock rates up to
4 000 0000 bits per second (4Mbps); other platforms and WIC 2A/S Serial interfaces may have a lower maximum clock rate.
Step 6: Record your general observations
Compare the different download times and video quality.
Step 7: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Step 8: Reflection
Consider and discuss how video and other data traffic can share network resources while maintaining
acceptable performance.
Video dan lalu lintas data dapat berbagi sumber daya jaringan yang sama jika bandwidth yang memadai tersedia atau jika lalu lintas yang diprioritaskan. Data lalu lintas dapat ditunda sedikit untuk memungkinkan lebih banyak waktu trafik video sensitif untuk memanfaatkan bandwidth yang tersedia.
Lab 4.5.1 Identifying Traffic Flows
Step 1: Cable and configure the current network
a. Referring to the topology diagram, connect the console (or rollover) cable to the console port on the
router and the other cable end to the host computer with a DB-9 or DB-25 adapter to the COM 1 port.
Ensure that power has been applied to both the host computer and router.
b. Establish a HyperTerminal or other terminal emulation program to the router.
c. From the command prompt on Host1, ping between Host1 and Discovery Server to confirm network
connectivity. Troubleshoot and establish connectivity if the pings fail.
Step 2: Configure NetFlow on the interfaces
From the global configuration mode, issue the following commands to configure NetFlow:
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode, issue the show ip flow interface command.
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-1#clear ip flow stats
Step 4: Create network data traffic
A range of network application data flows is to be generated and captured. Generate as many of the data
flows shown below as is possible in your lab. Your instructor will advise you of the particular applications that are available to be used in this lab.
a. Ping the Discovery Server from Host1 to generate a data flow.
From the command line of Host1, issue the command ping 172.17.1.1 -n 200
b. Telnet to the Discovery Server from Host1.
If Discovery Server is being used, issue the command telnet server.discovery.ccna from the
command prompt of Host1.
If Discovery Server is not being used, DNS is not configured , or if a terminal program such as
HyperTerminal or TeraTerm is being used, telnet from Host1 to 172.17.1.1.
c. On Host1, launch a web browser and enter the URL http://server.discovery.ccna
If Discovery Server is not being used or DNS is not configured, then use http://172.17.1.1 to access
the web services configured on that server.
d. Use FTP to download a file.
On Host1, launch a web browser and enter the URL ftp://server.discovery.ccna, or issue
ftp server.discovery.ccna from the command line. If DNS is not configured use the IP
address 172.17.1.1 instead of the domain name.
Download a file from the server.
e. If email accounts have been configured using the POP3 and SMTP services on Discovery Server,
send an email using one of these accounts.
Step 5: View the data flows
At the conclusion of the data flow, view the details by issuing the show ip cache flow command from privileged EXEC mode.
FC-CPE-1#show ip cache flow
Output similar to this will be displayed.
IP packet size distribution (3969 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .351 .395 .004 .011 .001 .005 .009 .001 .002 .005 .001 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .013 .000 .195 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
2 active, 4094 inactive, 1368 added
22316 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 17416 bytes
0 active, 1024 inactive, 0 added, 0 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 02:50:15
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 9 0.0 13 47 0.0 5.2 10.8
TCP-FTP 28 0.0 7 62 0.0 0.8 10.4
TCP-WWW 64 0.0 7 138 0.0 0.3 2.1
TCP-other 16 0.0 75 840 0.1 0.0 4.1
UDP-DNS 878 0.0 1 72 0.0 0.0 15.4
UDP-other 347 0.0 3 88 0.1 4.5 15.5
ICMP 26 0.0 1 70 0.0 0.8 15.4
Total: 1368 0.1 2 318 0.3 1.2 14.6
< output omitted >
From your output, list the name of each protocol with the number of flows. Answers vary. Examples shown.
Telnet 9 flows
FTP 28 flows
WWW 64 flows
DNS 878 flows
ICMP 26 flows
TCP other 16 flows
UDP other 347 flows
What was the total number of packets generated? 3969 packets
Which protocol generated the most packets? TCP other (75 x 16 = 1200)
Which protocol produced the most bytes per flow? TCP other (75 x 840 = 63000)
Which protocol’s flows were on the network the longest time? Telnet 5.2 sec
Which protocol used the longest amount of network time? UDP other (4.5 x 347 = 1561.5 sec)
Step 6: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Step 7: Reflection
Create a projected applications document listing the applications planned to use the network.
| Application Type | Application | Protocol | Prioritas | Comments |
| MS Outlook | SMTP | Menengah | Semua pengguna | |
| Voice | Call Manager/SIP | VRTP | Tinggi | Semua pengguna |
| Web | Apache Server | HTTP | Rendah | Semua pengguna |
| Database | SQL Server | TCP | Menengah | Restricted user |
Lab 4.5.2 Diagramming Intranet Traffic Flows
Step 1: Cable and configure the current network
a. Referring to the topology diagram, connect the console (or rollover) cable to the console port on the
router and the other cable end to the PC1 computer with a DB-9 or DB-25 adapter to the COM 1 port.
Ensure that power has been applied to both the host computer and router.
b. Establish a HyperTerminal or other terminal emulation program to the router.
c. Ping between Host1 and Host2 and between the hosts and Discovery Server to confirm network
connectivity. Troubleshoot and establish connectivity if the pings fail.
Step 2: Configure NetFlow on the interfaces
From the global configuration mode, issue the following commands to configure NetFlow:
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#end
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode, issue the show ip flow interface command.
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-1#clear ip flow stats
Step 4: Create network data traffic
A range of network application data flows between the Host1, Host2, and the server is to be generated and captured. Generate as many of the data flows shown below as is possible in your lab. Your instructor will advise you of the particular applications that are available to be used in this lab.
a. On Host1, launch a web browser and enter the URL http://server.discovery.ccna
b. On Host2, launch a web browser and enter the URL http://server.discovery.ccna
If Discovery Server is not being used, then use http://172.17.1.1 to access the web services
configured on that server.
c. Use FTP to download a file.
On Host1 and Host2, launch a web browser and enter the URL ftp://server.discovery.ccna,
or issue ftp server.discovery.ccna from the command line. If DNS is not configured, use the
IP address 172.17.1.1 instead of the domain name.
Download a file from the server.
d. If email accounts have been configured using the POP3 and SMTP services on Discovery Server,
send two emails between users on Host1 and Host2 using these accounts.
e. Set up Windows file sharing between Host1 and Host2 and copy a file from one to the other.
Step 5: View the data flows
At the conclusion of the data flow, view the details by issuing the show ip cache verbose flow
command from privileged EXEC mode.
FC-CPE-1#show ip cache verbose flow
| Application Type | Source | Destination | Comments |
| Web | Intranet Web Server | Host1 | |
| Web | Intranet Web Server | Host2 | |
| File Transfer | Intranet File Server | Host1 | |
| File Transfer | Intranet File Server | Host2 | |
| Host1 | Email Server | ||
| Host2 | Email Server | ||
| File Share | Host1 | Host2 |
Step 6: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Challenge
This lab simulates LAN data traffic. The LAN data flows of a production network would be much more
extensive and recorded over a greater period of time, perhaps a full working week.
a. On the FilmCompany initial current network topology shown on the next page, add PC host and
printer icons as listed for each VLAN. Draw a circle that encloses the local LAN segments.
b. Then, using the data flows recorded in this lab as a starting point, use different colors to mark the
different LAN data flows between hosts and the server.
Lab 4.5.3 Diagramming Traffic Flows to and from Remote Sites
Step 1: Cable and configure the current network
a. Cable the topology given in the diagram. Ensure that power has been applied to both the host
computer and router.
b. Establish a HyperTerminal or other terminal emulation program to the routers and configure the
hostname and interfaces shown in the table.
c. Set a clock rate on the DCE interface of the serial link between R2 and R3. Routing will have to be
configured on the three routers to establish data communications.
d. From PC1, ping and PC2 and Discovery Server to confirm network connectivity. Troubleshoot and
establish connectivity if the pings fail.
Step 2: Configure NetFlow on the router FC-CPE-1 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-1.
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-1, issue the show ip flow interface
command.
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-1#clear ip flow stats
Step 4: Configure NetFlow on the router FC-CPE-2 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-
2:
FC-CPE-2(config)#interface fastethernet 0/0
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-1(config-if)#interface serial 0/1/0
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#end
Step 5: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-2, issue the show ip flow interface
command.
FC-CPE-2#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-2#clear ip flow stats
Step 6: Configure NetFlow on the router ISP interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router ISP:
ISP(config)#interface fastethernet 0/1
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#interface serial 0/0/0
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#end
Step 7: Verify the NetFlow configuration
a. From the privileged EXEC mode on router ISP, issue the show ip flow interface command.
ISP#show ip flow interface
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
ISP#clear ip flow stats
Step 8: Create network data traffic
A range of network application data flows between the remote site, the FilmCompany LAN, and the network server is to be generated and captured. Generate as many of the data flows shown below as is possible in your lab. Your instructor will advise you of the particular applications that are available to be used in this lab.
a. On both PCs launch a web browser and enter the URL http://server.discovery.ccna
If Discovery Server is not being used, or DNS is not configured, then use http://172.17.1.1 to
access the web services configured on that server..
b. Use FTP to download a file.
On both PCs, launch a web browser and enter the URL ftp://server.discovery.ccna, or issue
ftp server.discovery.ccna from the command line. If DNS is not configured use 172.17.1.1
instead of the domain name. Download a file from the server.
c. If email accounts have been configured using the POP3 and SMTP services on Discovery Server,
send two emails in each direction between the user on the LAN and the Remote User using these
accounts.
d. To simulate data traffic between the two PCs, ping between them. Attempt to establish a Telnet
session between the two PCs. If file sharing has been enabled, copy a file in both directions between
the two.
Step 9: View the data flows
a. At the conclusion of the data flow, view the details by issuing the show ip cache verbose flow
command from privileged EXEC mode on each router.
FC-CPE-1#show ip cache verbose flow
FC-CPE-2#show ip cache verbose flow
ISP#show ip cache verbose flow
Router 1 – Sample Output
FC-CPE-1#show ip cache verbose flow
IP packet size distribution (1050 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .672 .278 .015 .000 .007 .000 .000 .000 .000 .000 .000 .001 .003 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.001 .000 .003 .011 .003 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
1 active, 4095 inactive, 150 added
2280 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
1 active, 1023 inactive, 27 added, 27 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:12:31
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-FTP 8 0.0 7 54 0.0 3.7 12.1
TCP-WWW 8 0.0 5 196 0.0 0.2 1.5
TCP-SMTP 16 0.0 15 72 0.3 15.8 1.7
TCP-other 32 0.0 11 77 0.5 2.2 1.5
UDP-DNS 49 0.0 5 67 0.3 6.1 15.6
UDP-other 38 0.0 1 83 0.0 0.0 15.4
Total: 151 0.2 6 77 1.4 4.3 10.2
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
FC-CPE-1#
Router 2 – Sample Output
FC-CPE-2#show ip cache verbose flow
IP packet size distribution (982 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .665 .164 .016 .000 .008 .000 .000 .000 .000 .000 .000 .002 .004 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.002 .000 .004 .128 .004 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
3 active, 4093 inactive, 145 added
2617 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
2 active, 1022 inactive, 50 added, 50 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:11:43
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 6 0.0 3 45 0.0 3.6 10.7
TCP-FTP 8 0.0 7 54 0.0 3.7 11.8
TCP-WWW 8 0.0 5 196 0.0 0.2 1.7
TCP-SMTP 16 0.0 15 72 0.3 15.8 1.6
TCP-other 32 0.0 11 77 0.5 2.2 1.4
UDP-DNS 8 0.0 1 69 0.0 0.1 15.3
UDP-other 59 0.0 1 55 0.0 0.0 15.4
ICMP 9 0.0 4 60 0.0 4.3 15.4
Total: 146 0.2 5 76 1.2 2.8 9.7
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
Fa0/1 0.0.0.0 Null 255.255.255.255 11 00 10 120
0044 /0 0 0043 /0 0 0.0.0.0 604 729.9
Se0/1/0 10.10.10.2 Null 224.0.0.9 11 C0 10 1
0208 /0 0 0208 /0 0 0.0.0.0 52 0.0
IPM: 0 0
FC-CPE-2#
Router 3 – Sample Output
ISP#show ip cache verbose flow
IP packet size distribution (502 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .709 .225 .015 .000 .007 .000 .001 .000 .000 .000 .000 .000 .007 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.003 .000 .003 .015 .007 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
1 active, 4095 inactive, 90 added
1274 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
1 active, 1023 inactive, 25 added, 25 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:11:21
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 6 0.0 3 45 0.0 3.6 10.7
TCP-WWW 8 0.0 5 196 0.0 0.2 1.5
TCP-SMTP 8 0.0 18 70 0.2 21.3 1.5
TCP-other 16 0.0 12 83 0.2 4.3 1.5
UDP-DNS 8 0.0 1 69 0.0 0.1 15.4
UDP-other 33 0.0 1 87 0.0 0.0 15.4
ICMP 10 0.0 4 60 0.0 5.4 15.5
Total: 89 0.1 5 85 0.7 3.6 10.1
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
Se0/1/0 10.10.10.1 Null 224.0.0.9 11 C0 10 1
0208 /0 0 0208 /0 0 0.0.0.0 92 0.0
IPM: 0 0
ISP#
b. Examine the output and record the different data flows for each router.
c. Discuss and compare the data flows for each router. Particularly consider how recording these flows
can assist in understanding which network devices and resources are used for particular flows.
Step 10: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Challenge
This lab simulates the flow of traffic to and from FilmCompany remote sites. These data flows for a production network would be much more extensive and recorded over a greater period of time, perhaps a full working week. Additionally, remote access would most likely be established using VPNs (Virtual Private Networks) across the Internet or a WAN. On the FilmCompany initial current network topology shown on the next page, add two remote site hosts attached to the “far” side of the cloud icon. Draw a circle that encloses the remote access links to the FilmCompany network and server. In this case study initially, the FilmCompany remote sites access its network across the Internet.
One of the objects of this analysis is to establish the benefits of using a dedicated WAN link using Frame
Relay for the stadium-based remote sites to access the FilmCompany network.
Using the data flows recorded in this lab as a starting point, use different colors to mark on the diagram the different data flows between the remote hosts and devices on the FilmCompany network.
Lab 4.5.4 Diagramming External Traffic Flows
Step 1: Cable and configure the current network
a. Cable the topology given in the diagram. Ensure that power has been applied to both the host
computer and router.
b. Establish a HyperTerminal or other terminal emulation program to the routers and configure the
hostname and interfaces shown in the table.
c. Set a clock rate on the DCE interface of the serial link between R2 and R3. Routing will have to be
configured on the three routers to establish data communications.
d. From PC1 ping both PC2 and Discovery Server to confirm network connectivity. Troubleshoot and
establish connectivity if the pings fail.
Step 2: Configure NetFlow on router FC-CPE-1 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-1.
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#end
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-1, issue the show ip flow interface
command.
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-1#clear ip flow stats
Step 4: Configure NetFlow on router FC-CPE-2 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-2:
FC-CPE-2(config)#interface fastethernet 0/0
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#interface fastethernet 0/1
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#interface serial 0/1/0
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#end
Step 5: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-2, issue the show ip flow interface
command.
FC-CPE-2#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-2#clear ip flow stats
Step 6: Configure NetFlow on router ISP interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router ISP:
ISP(config)#interface fastethernet 0/1
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#interface serial 0/1/0
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#end
Step 7: Verify the NetFlow configuration
a. From the privileged EXEC mode on router ISP, issue the show ip flow interface command.
ISP#show ip flow interface
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are reset:
ISP#clear ip flow stats
Step 8: Create network data traffic
A range of Internet application data flows between PC2 (the Internet) and the FilmCompany network is to be generated and captured. Generate as many of the data flows shown below as it is possible in your lab. Your instructor will advise you of the particular applications that are available and to be used in this lab.
a. On PC2, launch a web browser and enter the URL http://server.discovery.ccna
If Discovery Server is not being used, or DNS is not configured, then use http://172.17.1.1 to
access the web services configured on that server.
b. Use FTP to download a file.
On PC2, launch a web browser and enter the URL ftp://server.discovery.ccna, or issue ftp
server.discovery.ccna from the command line. If DNS is not configured use the IP address
172.17.1.1 instead of the domain name. (example: http://172.17.1.1 )
Download a file from the server.
c. If email accounts have been configured using the POP3 and SMTP services on Discovery Server,
send two emails from PC2 using these accounts.
Step 9: View the data flows
a. At the conclusion of the data flow, view the details by issuing the show ip cache verbose flow
command from privileged EXEC mode on each router.
FC-CPE-1#show ip cache verbose flow
FC-CPE-2#show ip cache verbose flow
ISP#show ip cache verbose flow
b. Examine the output and record the different data flows for each router.
c. Discuss and compare the data flows for each router. Particularly consider how these flows differ from
Lab 4.5.3 and the implications this has in understanding which network devices and resources are
used for particular flows.
Step 10: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Challenge
This lab simulates the flow of traffic to and from FilmCompany network and the Internet. These data flows for a production network would be much more extensive and recorded over a greater period of time, perhaps a full working week. On the FilmCompany initial current network topology shown on the next page, highlight the network Internet link. Using the data flows recorded in this lab as a starting point, use different colors to mark on the diagram the different possible data flows between the hosts and devices on the FilmCompany network to and from the Internet.
Lab 4.5.5 Diagramming Extranet Traffic Flows
Step 1: Cable and configure the current network
a. Cable the topology given in the diagram. Ensure that power has been applied to both the host
computer and router.
b. Establish a HyperTerminal or other terminal emulation program to the routers and configure the
hostname and interfaces shown in the table.
c. Set a clock rate on the DCE interface of the serial link between R2 and R3. Routing will have to be
configured on the three routers to establish data communications.
d. From PC1, ping PC2 and Discovery Server to confirm network connectivity. Troubleshoot and
establish connectivity if the pings fail.
Step 2: Configure NetFlow on router FC-CPE-1 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-1.
FC-CPE-1(config)#interface fastethernet 0/0
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#interface fastethernet 0/1
FC-CPE-1(config-if)#ip flow ingress
FC-CPE-1(config-if)#ip flow egress
FC-CPE-1(config-if)#end
Step 3: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-1, issue the show ip flow interface
command.
FC-CPE-1#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-1#clear ip flow stats
Step 4: Configure NetFlow on router FC-CPE-2 interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router FCCPE-2:
FC-CPE-2(config)#interface fastethernet 0/0
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#interface fastethernet 0/1
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#interface serial 0/1/0
FC-CPE-2(config-if)#ip flow ingress
FC-CPE-2(config-if)#ip flow egress
FC-CPE-2(config-if)#end
Step 5: Verify the NetFlow configuration
a. From the privileged EXEC mode on router FC-CPE-2, issue the show ip flow interface
command.
FC-CPE-2#show ip flow interface
FastEthernet0/0
ip flow ingress
ip flow egress
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
FC-CPE-2#clear ip flow stats
Step 6: Configure NetFlow on router ISP interfaces
From the global configuration mode, issue the following commands to configure NetFlow on the router ISP:
ISP(config)#interface fastethernet 0/1
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#interface serial 0/1/0
ISP(config-if)#ip flow ingress
ISP(config-if)#ip flow egress
ISP(config-if)#end
Step 7: Verify the NetFlow configuration
a. From the privileged EXEC mode on router ISP, issue the show ip flow interface command.
ISP#show ip flow interface
FastEthernet0/1
ip flow ingress
ip flow egress
Serial0/1/0
ip flow ingress
ip flow egress
Confirm that the output shown above is displayed. Troubleshoot your configuration if this output is not
displayed.
b. From the privileged EXEC mode, issue the following command to ensure that flow cache statistics are
reset:
ISP#clear ip flow stats
Step 8: Create network data traffic
Ideally, a range of network application data flows between the trusted extranet host PC2 and PC1 on the
FilmCompany LAN should be generated and captured. Generate as many of the data flows shown below as is possible in your lab. Your instructor will advise you of the particular applications that are available and to be used in this lab.
To simulate data traffic between the two PCs:
a. Ping between them.
b. Attempt to establish a Telnet session between the two PCs.
c. If you have rights, enable file sharing and copy a file in both directions between the two PCs.
Step 9: View the data flows
a. At the conclusion of the data flow, view the details by issuing the show ip cache verbose flow
command from privileged EXEC mode on each router.
FC-CPE-1#show ip cache verbose flow
FC-CPE-2#show ip cache verbose flow
ISP#show ip cache verbose flow
Router 1 – Output
FC-CPE-1#show ip cache verbose flow
IP packet size distribution (12 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .000 1.00 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .000 .000 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
0 active, 4096 inactive, 12 added
192 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
0 active, 1024 inactive, 8 added, 8 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:03:38
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
UDP-DNS 2 0.0 1 70 0.0 0.0 15.7
UDP-other 10 0.0 1 87 0.0 0.0 15.5
Total: 12 0.0 1 84 0.0 0.0 15.5
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
FC-CPE-1#
Router 2 – Output
FC-CPE-2#show ip cache verbose flow
IP packet size distribution (5223 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .303 .030 .142 .031 .034 .001 .002 .001 .000 .000 .004 .000 .075 .000
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .020 .351 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
9 active, 4087 inactive, 62 added
1970 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
0 active, 1024 inactive, 20 added, 20 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:04:31
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 18 0.0 3 45 0.2 3.6 10.9
TCP-other 4 0.0 1 40 0.0 0.0 15.5
UDP-DNS 2 0.0 1 70 0.0 0.0 15.4
UDP-other 22 0.0 1 53 0.0 0.0 15.3
ICMP 8 0.0 14 60 0.4 13.9 15.2
Total: 54 0.2 3 54 0.7 3.2 13.8
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
Fa0/1 0.0.0.0 Null 255.255.255.255 11 00 10 222
0044 /0 0 0043 /0 0 0.0.0.0 604 1356.9
Fa0/1 10.0.0.200 Se0/1/0 10.20.0.200 06 00 18 1368
01BD /0 0 06AA /0 0 0.0.0.0 970 184.9
Fa0/1 10.0.0.200 Se0/1/0* 10.20.0.200 06 00 18 1368
01BD /0 0 06AA /0 0 0.0.0.0 970 184.9
FFlags: 01
Se0/1/0 10.20.0.200 Fa0/0 172.17.1.1 11 00 10 5
0404 /0 0 0035 /0 0 0.0.0.0 62 4.3
Se0/1/0 10.20.0.200 Fa0/0* 172.17.1.1 11 00 10 5
0404 /0 0 0035 /0 0 0.0.0.0 62 4.3
FFlags: 01
Fa0/0 172.17.1.1 Se0/1/0* 10.20.0.200 11 00 10 5
0035 /0 0 0404 /0 0 0.0.0.0 62 4.3
FFlags: 01
Fa0/0 172.17.1.1 Se0/1/0 10.20.0.200 11 00 10 5
0035 /0 0 0404 /0 0 0.0.0.0 62 4.3
Se0/1/0 10.20.0.200 Fa0/1 10.0.0.200 06 00 18 1152
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
06AA /0 0 01BD /0 0 0.0.0.0 71 184.9
Se0/1/0 10.20.0.200 Fa0/1* 10.0.0.200 06 00 18 1210
06AA /0 0 01BD /0 0 0.0.0.0 71 194.7
FFlags: 01
Fa0/0 10.10.0.1 Null 224.0.0.9 11 C0 10 1
0208 /0 0 0208 /0 0 0.0.0.0 52 0.0
IPM: 0 0
FC-CPE-2#
Router 3 – Output
ISP#show ip cache verbose flow
IP packet size distribution (6724 total packets):
1-32 64 96 128 160 192 224 256 288 320 352 384 416 448 480
.000 .306 .029 .138 .031 .032 .001 .001 .001 .000 .000 .003 .000 .080 .001
512 544 576 1024 1536 2048 2560 3072 3584 4096 4608
.000 .000 .000 .008 .362 .000 .000 .000 .000 .000 .000
IP Flow Switching Cache, 278544 bytes
5 active, 4091 inactive, 54 added
1881 ager polls, 0 flow alloc failures
Active flows timeout in 30 minutes
Inactive flows timeout in 15 seconds
IP Sub Flow Cache, 21640 bytes
1 active, 1023 inactive, 12 added, 12 added to flow
0 alloc failures, 0 force free
1 chunk, 0 chunks added
last clearing of statistics 00:05:44
Protocol Total Flows Packets Bytes Packets Active(Sec) Idle(Sec)
——– Flows /Sec /Flow /Pkt /Sec /Flow /Flow
TCP-Telnet 18 0.0 3 45 0.1 3.6 10.7
TCP-other 4 0.0 1 40 0.0 0.0 15.7
UDP-DNS 4 0.0 3 63 0.0 2.1 15.5
UDP-other 16 0.0 1 77 0.0 0.0 15.4
ICMP 8 0.0 14 60 0.3 13.4 15.5
Total: 50 0.1 4 58 0.6 3.6 13.7
SrcIf SrcIPaddress DstIf DstIPaddress Pr TOS Flgs Pkts
Port Msk AS Port Msk AS NextHop B/Pk Active
Se0/1/0 10.0.0.200 Fa0/1 10.20.0.200 06 00 18 1794
01BD /0 0 06AA /0 0 0.0.0.0 989 245.1
Se0/1/0 10.0.0.200 Fa0/1* 10.20.0.200 06 00 18 1794
01BD /0 0 06AA /0 0 0.0.0.0 989 245.1
FFlags: 01
Fa0/1 10.20.0.200 Se0/1/0 10.0.0.200 06 00 18 1502
06AA /0 0 01BD /0 0 0.0.0.0 69 245.0
Fa0/1 10.20.0.200 Se0/1/0* 10.0.0.200 06 00 18 1502
06AA /0 0 01BD /0 0 0.0.0.0 69 245.0
FFlags: 01
ISP#
b. Examine the output and record the different data flows for each router.
c. Discuss and compare the data flows for each router. Particularly consider how these flows differ from
the previous Labs and the implications this has in understanding which network devices and
resources are used for particular flows.
Step 10: Clean up
Erase the configurations and reload the routers and switches. Disconnect and store the cabling. For PC hosts that are normally connected to other networks (such as the school LAN or to the Internet), reconnect the appropriate cabling and restore the TCP/IP settings.
Challenge
This lab simulates the flow of traffic to and from FilmCompany and from selected trusted partners and
customers. These data flows for a production network would be much more extensive and recorded over a greater period of time, perhaps a full working week. Additionally, remote access from trusted sites would most likely be established using VPNs (Virtual Private Networks) across the Internet or a WAN.
On the FilmCompany initial current network topology shown on the next page, add two trusted remote site
hosts attached to the “far” side of the cloud icon. Draw a circle that encloses the remote access links to the FilmCompany network and server. In this case study, initially the FilmCompany remote sites access its network across the Internet. One of the objects of this analysis is to establish the benefits of using a dedicated WAN link using Frame Relay for the stadium-based remote sites to access the FilmCompany network. Then, using the data flows recorded in this lab as a starting point, use different colors to mark on the diagram the different extranet data flows between the trusted remote hosts and devices on the FilmCompany network. Diagram traffic flows to and from selected trusted partners, customers, and vendors.



0 komentar:
Posting Komentar